Cloud Security Risk Management Approach And Procedures

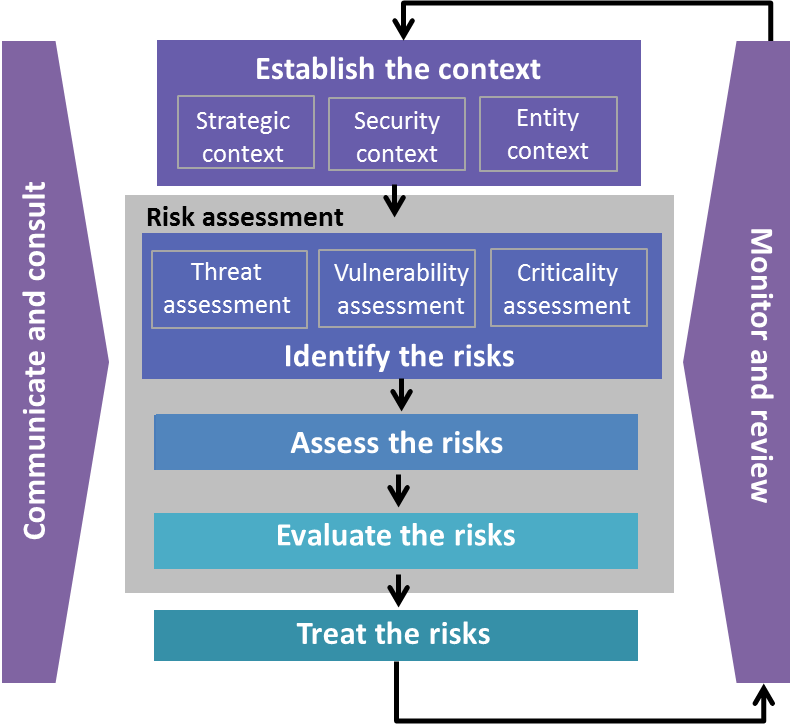
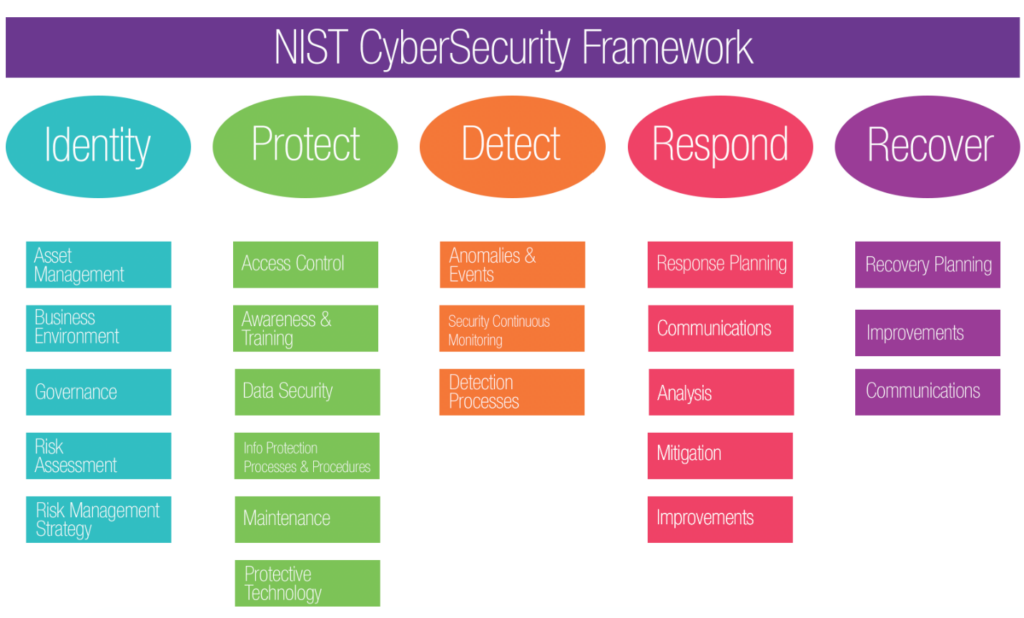
Each regulated entity should use a risk based approach across key areas listed below to meet fhfa supervisory expectations.
Cloud security risk management approach and procedures. Management must buy or build management and security in the cloud information risk and security as well as its monitoring and. We ll be discussing how gc agencies and departments are cracking down on cloud security in order to handle risks in an effective manner. Government of canada cloud security risk management approach and procedures treasury board of canada secretariat cccs itsp 30 031 v2 user authentication guidance for information technology systems. Protect your most valuable data in the cloud and on premises with oracle s security first approach.
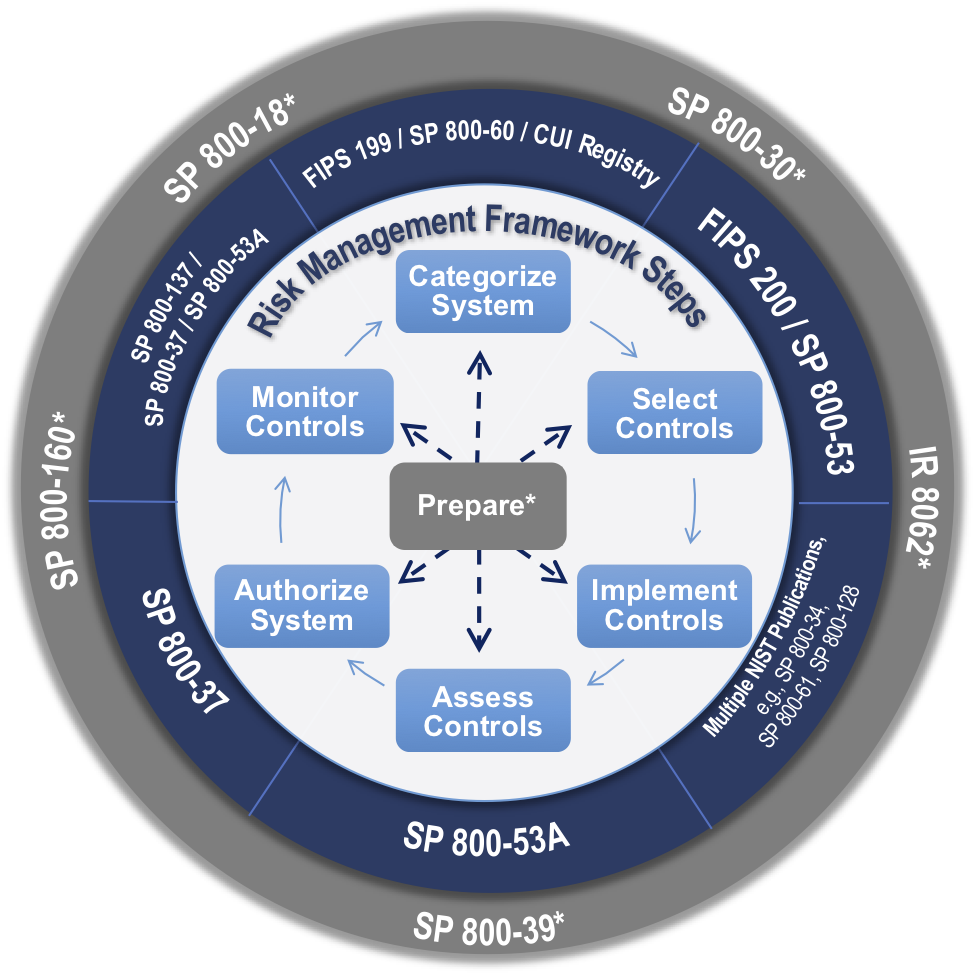
And procedures documented approved and implemented. Under the cloud computing paradigm the gc will depend on vendors for many aspects of security and privacy and in doing so will confer a level of trust onto the cloud service provider csp. Gc approach to cloud security risk management. Oracle has decades of experience securing data and applications.
Cloud services have become readily available to individuals and organizations. Help keep your organization secure and compliant with google cloud. To establish this trust the gc requires an information system security risk management approach and procedures that are adapted to cloud computing. Effective risk management of cloud providers is critical to safe and sound operations.
Risk mitigation planning is the process of developing options and actions to enhance opportunities and reduce threats to project objectives 1. Even the government of canada uses cloud service providers on a regular basis. Security identity and compliance. After the first review round the top risks have turned out to be more or less unchanged from the 2009 cloud risk assessment.
Responsibilities of the board and senior management. Learn about our privacy and security practices cloud compliance offerings and more. Oracle cloud infrastructure delivers a more secure cloud to our customers building trust and protecting their most valuable data. Strategies policies procedures and internal standards.
1 4 top security risks the 2009 cloud risk assessment contains a list of the top security risks related to cloud computing. In addition the standard goes beyond confidentialityand also covers availability and integrity all. Standard follows a risk based approach to prioritizing security empha ses and contains practical data control strategies. Risk mitigation progress monitoring includes tracking identified risks identifying new risks and evaluating risk process effectiveness throughout the.
Risk management for cloud computing.